No company wants to be subjected to a cyberattack or security threat, so protecting your digital information and technology is critical. Though there are countless information security frameworks and assessments available, the HITRUST CSF and HITRUST Validated Assessments with Certification are often regarded as the gold standard.
So what is the HITRUST CSF?
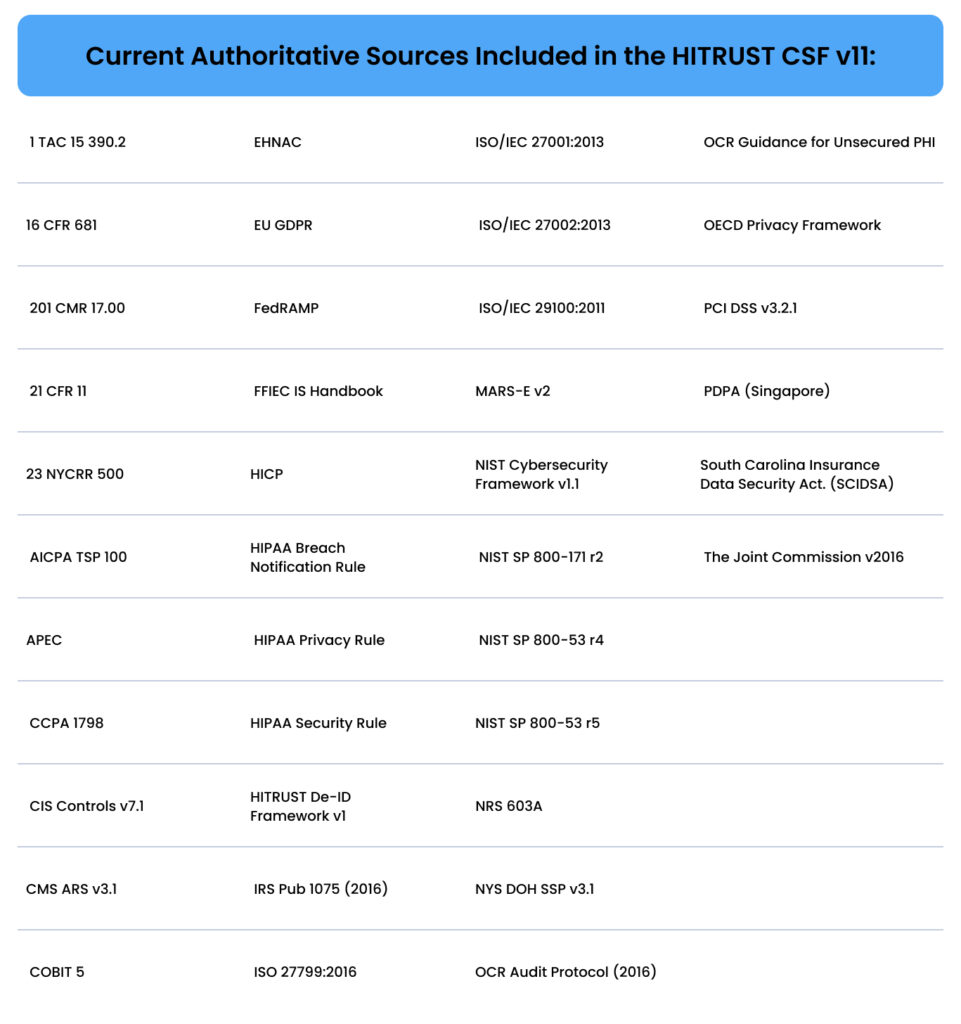
The HITRUST CSF is a globally utilized and recognized framework that includes dozens of authoritative sources covering multiple industries. The CSF unifies and harmonizes many authoritative sources, pre-existing security regulations, and frameworks — such as NIST, HIPAA, ISO 27001, FedRAMP, PCI DSS, GDPR, and dozens of others.
Implementing the HITRUST CSF is a critical step towards preventing your company from becoming vulnerable to cyber-attacks and providing greater stakeholder confidence.
The HITRUST CSF
The HITRUST CSF framework was developed and continues evolving to measure and manage security risks with greater objectivity and reliability. The CSF helps organizations meet information security challenges by identifying and managing robust security and privacy controls. The CSF unifies and harmonizes many authoritative sources, industry standards, and security regulations, so it is truly one of the broadest compliance frameworks available.
Using the CSF framework foundation, HITRUST Certification allows nearly any organization, regardless of size or sector, to prove that its cybersecurity program meets recognized industry standards and regulations.
How can my organization obtain HITRUST Certification?
Becoming fully HITRUST Certified requires an independent assessment from a HITRUST-Authorized External Assessor. The time it takes to complete the HITRUST Certification process can take six (6) to eighteen (18) months, depending on the nature of your organization, the assessment you select, and the current strength of your information security program.
Below are the five (5) primary steps it takes to obtain HITRUST Certification. Getting started on these steps helps your organization get ready for the assessment process. And knowing what to expect during the certification process can set up a smoother, more efficient experience.
If you are considering HITRUST Certification and have questions or need guidance, we are happy to walk you through the assessment process.
HITRUST certification steps:
- Download the HITRUST CSF framework free of charge from the HITRUST website
- Perform a readiness assessment (e1, i1, or r2) using the MyCSF SaaS platform
- Select an authorized HITRUST External Assessor (aka a licensed third-party auditor)
- Undergo a HITRUST Validated Assessment (e1, i1, or r2) via MyCSF
- Receive your HITRUST letter of certification (if review is passed)

It’s important to remember that the certification steps shown are just general broad-stroke guidelines. When it comes to getting HITRUST Certified, each organization will have its own unique situations and circumstances. If you need any help, make sure to reach out to an expert.
What are the HITRUST CSF control categories?
There are 14 HITRUST CSF control categories with 49 objectives and 156 control references (135 for security and 21 for privacy). Each category has a designated objective (desired result) and multiple specifications (policies, guidelines, practices, etc.) There are up to three levels of implementation for control requirements and there are nearly 2000 requirement statements included in the HITRUST CSF. However, based on risk and regulatory requirements, only a subset of the total list will be in scope for your organization.
Note: This list of controls is not in order of importance, as all controls are considered equally important.
- Information Security Management Program
- Access Control
- Human Resources Security
- Risk Management
- Security Policy
- Organization of Information Security
- Compliance
- Asset Management
- Physical and Environmental Security
- Communications and Operations Management
- Information Systems Acquisition, Development, and Maintenance
- Information Security Incident Management
- Business Continuity Management
- Privacy Practices
Each of the above HITRUST CSF controls is assessed based on the following five PRISMA maturity levels
- Policy
- Procedure
- Implemented
- Measured
- Managed
The PRISMA maturity levels evaluated differ based on the HITRUST Assessment selected.
Who needs a HITRUST CSF Validation with Certification?
A HITRUST Validated (+ Certification) Assessment can benefit just about any organization in any sector. Meeting HITRUST Certification standards establishes premium security standards for data security and IT system protection to build confidence with both internal and external stakeholders
Because the HITRUST Validation process is so effective in the healthcare sector, many providers and payers not only achieve HITRUST Certification in their own organization but also require their vendors who handle sensitive data to become HITRUST Certified. As a result, HITRUST Certification has become a leading industry standard in the healthcare community ecosystem.
What does the HITRUST CSF Validation with Certification cost?
Given its depth and complexity, assessor costs for a HITRUST Certification require a significant investment. Costs differ by type of assessment and vary greatly depending on the size and scale of an organization, and the maturity of the existing cybersecurity program. Accessor costs can range between $36,000 to nearly $200,000, and there is also a HITRUST report credit required. Conducting a readiness assessment without an External Assessor saves much of the cost; however, the level of security assurance also decreases because it is not independently verified, so it’s highly recommended that you work with an Approved External Assessor when embarking on your HITRUST journey. When it comes to protecting sensitive data, it’s important to conduct a thorough assessment of your own needs and not jump to saving costs as the primary objective.

Even if a HITRUST Validated Assessment and Certification is not possible to achieve at the outset, qualifying organizations can download and begin using the HITRUST CSF free of charge. The framework can help get started meeting many important security goals. However, to get the full value from the HITRUST CSF, you’ll still need to do more work to become HITRUST Certified.
How does the HITRUST CSF drive the HITRUST approach?
The HITRUST Approach leverages integrated, modular solutions to create a standardized and comprehensive information risk management and compliance program.
With the HITRUST CSF at the foundation, the HITRUST Approach offers a single proven methodology that includes components that are consistent, aligned, and maintained. Once the framework is implemented, it provides the foundation that continues to support, build, and improve an organization’s information risk management and compliance program.
The HITRUST Approach integrates:
- HITRUST CSF — a robust privacy and security controls framework
- HITRUST Assurance Program — a scalable and transparent means to provide reliable assurances to internal and external stakeholders
- HITRUST MyCSF — an assessment and corrective action plan management SaaS platform
- HITRUST Threat Catalogue — a list of reasonably anticipated threats mapped to specific CSF controls
- HITRUST Assessment XChange — a third-party risk management solution that is both comprehensive and modular, including the three vital components of people, process, and technology, to streamline and simplify third-party risk management
- HITRUST Shared Responsibility and Inheritance Program — means to automatically import prior HITRUST control assessment testing results and scoring that are available from providers of internal shared IT services and external cloud-hosted services, supported by a suite of matrices that clarify shared responsibilities
- HITRUST Third-Party Assurance Program — a third-party risk management process
- HITRUST Academy — a comprehensive training program designed to educate about
Which authoritative sources does the HITRUST CSF cover?
When an organization embarks on getting HITRUST Certified, it’s helpful to know exactly how sophisticated the HITRUST CSF framework is. (We can assure you, it’s highly comprehensive and refined!)
Below you’ll find the list of dozens of information security and privacy-related industry authoritative sources, frameworks, and standards harmonized into the HITRUST CSF (as of version 11.0.0).
Is HITRUST compliance right for your organization?
With the evolution of technology each passing year, getting compliant via the HITRUST CSF is becoming even more essential. Shielding your business from data theft and secure information breaches will keep what’s most important out of harm’s way. HITRUST CSF Validation will ensure your organization is both present- and forward-thinking when it comes to complete protection.
HITRUST keeps on top of any regulation changes as they unfold, always ensuring that the highest standard of data security is being achieved. By staying up to date, HITRUST protects an organization’s sensitive information and reduces its risk by assisting with internal and external risk management.
Being certified demonstrates that your organization prioritizes digital security and privacy, which builds trust inside and out. HITRUST’s streamlined framework helps simplify compliance for your business, both now and in the future.
If you believe that getting HITRUST certified is correct for your business, we can help guide you toward success. Talk to an expert today.
HITRUST Guide
Get the HITRUST Guide for Health Tech companies
The future of health tech is HITRUST! Get ahead of the curve and understand the how and why of HITRUST in this in-depth guide.

Related Posts
Stay connected
Subscribe to receive new blog articles and updates from Thoropass in your inbox.
Want to join our team?
Help Thoropass ensure that compliance never gets in the way of innovation.













.png)