The Payment Card Industry Data Security Standard (PCI DSS) was co-founded in 2006 by the major credit card processing networks to help businesses and financial institutions protect themselves and others from breaches, data theft, and fraud. Since then, PCI DSS has evolved to counter emerging security threats, with the latest iteration, PCI DSS 4.0, going into effect in March 2024.
But it’s not just PCI DSS that evolves. As your client base expands, so do their security demands, and the consequences of data breaches grow more severe. Potential clients are constantly evaluating your security measures. Some may be less concerned about compliance. But the accounts that are critical to achieving your quarterly goals and advancing your vision are meticulously assessing your offerings for warning signs and positive indicators. Here’s a rundown of what they’re looking for so that you can instill confidence and ensure your security posture isn’t a dealbreaker.
Red flags: areas to address
Lack of secure authentication
Passwords alone are now insufficient to protect user accounts. With the rise of data breaches and password-related incidents, implementing multi-factor authentication (MFA) is crucial. MFA requires users to provide more than a password for account access, significantly enhancing security. It’s now universally accepted in personal and professional settings.
MFA solutions help businesses secure user accounts by requiring additional validation via authentication factors like one-time passcodes, mobile push, and biometric factors. G2’s Guide to the Best MFA Software is a trusted place to start exploring.
To enforce strong password policies and enhance security, IT administrators use solutions that prevent users from creating weak passwords. These solutions also check passwords against blacklists and dictionary hacks. Explore G2’s rundown of the Best Password Policy Enforcement Software to enhance your organization’s password policies and complexity rules.
Unencrypted data storage
Storing sensitive customer data without robust encryption makes it instantly readable to anyone who gains access and is a security risk. Hackers actively target unencrypted data sources, exploiting vulnerabilities to steal sensitive information such as social security numbers and bank details.
Prospective users can quickly identify whether your site is encrypted by looking for the “https” prefix in your URL. They may also look for the padlock icon in their web browser’s address bar, indicating that their browser’s connection with your site is secure.
Patch management delays
Patch management is the process of regularly updating software, drivers, and firmware to protect against security vulnerabilities and ensure systems operate optimally. Delayed application of security patches leaves your business and customers vulnerable to potential attacks. Timely patching is crucial to maintaining a secure environment.
Limited endpoint security
Endpoint security is the practice of safeguarding data and workflows associated with end-user devices that connect to your network. Inadequate security on these devices provides cybercriminals with potential entry points for attacks. Endpoint protection platforms (EEPs) examine files as they enter your network, helping identify and mitigate threats. To explore EEP solutions, refer to trusted resources like Capterra.
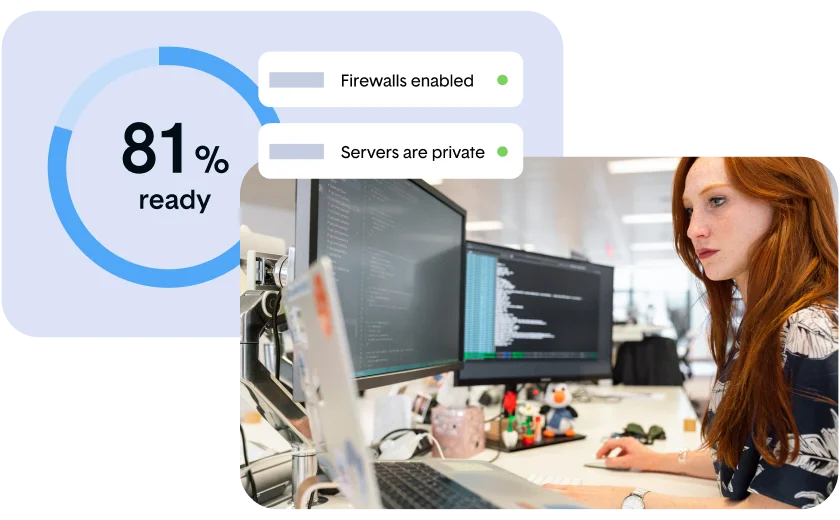
Sparse security infrastructure
Infrastructure security encompasses how your business protects critical systems and assets against threats. It involves securing hardware and software assets, such as end-user devices, data center resources, networking systems, and cloud resources.
Without a robust security infrastructure, your proprietary data and intellectual property are at risk of loss and disruption. Prospective customers look for core security measures — like intrusion detection and network monitoring — to ensure you’re a secure and reliable partner.

Recommended for you
The 12 requirements of PCI DSS: your compliance checklist
If you’re pursuing PCI DSS, it’s essential to understand the 12 requirements and what’s expected of your business.
Green flags: best practices to embrace
Comprehensive data encryption
End-to-end encryption (E2EE) is the gold standard in data transfer security, ensuring that only authorized parties with decryption keys can access and decipher encrypted data during transit between endpoints. Its impenetrable security protocol leaves no room for unauthorized access or tampering, making it a vital assurance of data integrity and confidentiality.
E2EE symbolizes an organization’s unwavering commitment to data security, gaining the trust of partners and clients. Many IT decision-makers consider E2EE non-negotiable in security service level agreements (SLAs), making it a cornerstone for building secure partnerships and confidently conducting critical transactions. E2EE isn’t just a best practice. It’s a strategic imperative that separates trustworthy solutions from the rest, safeguarding sensitive information and instilling security at every level of interaction.
Regular security training
With 88% of data breach incidents caused by employees’ mistakes, regular security awareness training is a critical defense against cyber threats. Businesses that invest in employee training reduce the likelihood of breaches and accelerate their ability to detect and isolate a violation.
Security training is not a one-time event; it should be an ongoing process. The Information Systems Audit and Control Association (ISACA) recommends cybersecurity awareness training every four to six months to keep security top-of-mind for employees. Communicating the regularity of your training efforts to customers can reassure them that security is your top concern.
Active threat intelligence
Threat intelligence is data containing detailed knowledge about cybersecurity threats targeting an organization. It is always organization-specific, detailed, and actionable, enabling security teams to proactively prevent, detect, and respond to cyber-attacks. Organizations that harness threat intelligence are better equipped to defend against evolving threats.
Fortunately, threat intelligence services can support your team by delivering knowledge, information, and data about your potential blind spots. These services help you make informed decisions that reduce your risk and the likelihood of facing a security breach.
Incident response
Organizations that prioritize security use incident response plans (IRPs) to document internal processes and technologies for detecting and responding to cyber threats, security breaches, or cyberattacks. A clear, tested IRP communicates to potential partners that you’re prepared to quickly contain cyber threats, restore affected systems, and reduce lost revenue, regulatory fines, and other associated costs.
According to IBM’s Cost of a Data Breach 2022 Report, organizations with dedicated incident response teams and regularly tested plans had an average data breach cost of USD 2.66 million lower than those without incident response teams and IRPs. The finding underscores the importance of incident response readiness and why it’s critical for buyers.
Ongoing compliance auditing
Continuous auditing to comply with security standards, such as PCI DSS, signals to buyers that you’re committed to maintaining secure operations. While compliance is indeed a good and essential thing, it can be perceived internally as a blocker to innovation.
In 2019, Thoropass was born with the sole mission of eliminating that tradeoff. We offer automated compliance monitoring and data collection in one robust solution so you can reach and maintain your compliance goals now and as you grow. Book time with a compliance expert to learn more about us and how The OrO™ Way approach can strengthen and protect your business.
Emphasizing security in your business strategy
Avoiding the red flags and demonstrating the green ones means the difference in building and maintaining trust with your partners and attracting new ones. Demonstrating your commitment to security isn’t just about compliance — it’s about adopting best practices to protect your organization and customers. To get more insight into how your organization is tracking, tools like our interactive Compliance Mix Quiz can help. It takes a few minutes to start on your organization’s best and most efficient path to complete compliance and assure the safety and security of your customers’ data.
PCI DSS
Start your PCI DSS compliance journey today
Manage everything you need to become PCI DSS compliant, all within one easy to use platform.
Related Posts
Stay connected
Subscribe to receive new blog articles and updates from Thoropass in your inbox.
Want to join our team?
Help Thoropass ensure that compliance never gets in the way of innovation.













.png)